Reflections Upon a SWATting

October 16th, 2017 started off like any other Monday. I awoke at 6 AM and drove to the YMCA to play racquetball, ready to start the week with a win.
When I finished playing, I tweeted out a cute quip:
When you wake up and realize it's Monday and there's still a whole month of SegWit2X drama ahead of us. pic.twitter.com/c6PjV6Q8e8
— Jameson Lopp (@lopp) October 16, 2017
I then hit the steam room and the shower to relax and freshen up. Upon returning to my neighborhood, I encountered an unusual problem: a police cruiser with its lights flashing was blocking the entrance. I came to a stop and rolled down my window:
“Hi Officer, is there a problem? I’m just trying to get to my house.”
“Sorry, we have to secure the area due to an ongoing incident.”
“Is it an active shooter?”
“Unclear, but we have information that he has long guns on the premises.”
“Well shit, what should I tell my family to do? They’re at the house.”
“Call them and tell them to get in the car and exit the community.”
“Will do!”
I pulled off the main road and found a place to park so that I could call the house.
“Hey, don’t panic but the police are locking down the neighborhood due to an incident. You should get in the car and leave.”
“OK, I’ll be right out.”
I waited a few minutes and then received a call back.
“The police stopped me as I was leaving and asked me if I was OK. Apparently they were called to our house! They want you to come speak with them at the mobile command unit around the corner.”
I drove back to the entrance and told the patrol officer that his captain wanted to speak with me, so he waved me through. Upon entering the mobile command unit, the first thing I was asked was
“Sir, do you have any enemies?”
To which I replied:

It wasn’t long before the news stations showed up; apparently they didn’t even know what “swatting” means. It wasn't long before the incident was on the evening news, web sites, and social media.
The news stations managed to get a copy of the phone call that was made by the attacker; you can listen to it here. The attacker claimed that they shot and killed someone and were holding others hostage after rigging the front door with explosives.
Once the news crews left and everything calmed down, I figured I should let the attacker know that they failed to achieve their goal.
Dear anonymous coward who just sent dozens of cops w/ rifles to my house w/a false hostage situation report: I am not so easily intimidated.
— Jameson Lopp (@lopp) October 16, 2017
Within a few hours of making my tweet, I received a threatening voicemail from a number with a New York area code; you can listen to the voicemail here. Note a common theme between the 911 call and the voicemail — both times he demands $50,000 (or the equivalent in BTC.)
“Next time I do anything to you, it won’t involve the police.”
Within 48 hours the Durham Police Department told me that they had traced the call to a throwaway server in Texas but hit a dead end and were turning the case over to the FBI. I never heard from the FBI. I lost any confidence in the ability of law enforcement to protect me a long time ago, so this was disappointing but not surprising.
What did I do in response? I installed 360º 4K resolution surveillance around my property, double checked the rest of my physical security setup, took a few firearms out of the safe, and I waited.
When assholes are making threats against your life but this replay protection code ain't gonna write itself. pic.twitter.com/d4MLox4kwd
— Jameson Lopp (@lopp) October 18, 2017
Fortunately, my intuition that the attacker didn’t have the guts to put his own life in danger by physically attacking me proved to be right. There were no further (physical) incidents.
Shit Just Got Real
Swatting is not a game; it can be fatal. Case in point, where an innocent man was killed by police during a SWATting.
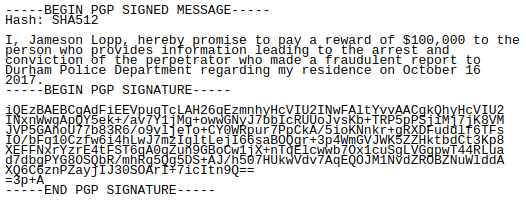
I have little hope that the perpetrator will be found, but I feel compelled to offer an additional incentive. I want to make it extremely clear that I will not tolerate threats against myself or anyone I care about. I will defend myself and my loved ones until my dying breath with every resource at my disposal. The following message is signed with this PGP key.
There was a lot of speculation that this was related to the Bitcoin scaling debate, but the attacker never said what his motivations were. After the fact, he left me this voicemail demanding a ransom payment… but didn’t even give me an address to which I should send the BTC! After speaking with other folks who have been harassed, I fully expected other annoyances such as:
- Using stolen credit cards to purchase things and ship them to my house.
- Purchasing drugs / illegal things on darknet sites and shipping them to my house.
- Tampering with the accounts for my utilities to get them turned off.
- Forging a deed in an attempt to claim ownership of my home.
On November 9, I got email bombed by a bot that was signing me up for a ton of email marketing lists. Since the emails were “legitimate” marketing rather than mass emails from a few sources, I decided pretty quickly that the best option was to just I turn off my email for the day and made most of the signups bounce, preventing my email address from getting added to the lists of the marketers. I guess 8 years of experience writing email marketing software has its perks.
12 hours later statoshi.info was DoS attacked and my host blackholed the IP address to save their own infrastructure. No big deal.
https://t.co/fbDePthEQH will be unavailable until further notice - when the DoS attack ends. I have more patience than you do, attacker. 😉
— Jameson Lopp (@lopp) November 9, 2017
A Few Thoughts on OPSEC
I’ve kept this detail a secret for the past year, but I wasn’t home when the attacker sent the SWAT team to my house. I truly hope that the perpetrator reads this article and gets to realize how miserably they failed.
I highly suspect that the reason the attacker chose to strike when he did was from the tweet you see at the beginning of this article. I generally vary my social media posts and delay tweeting anything that may tie me to a specific location. So when the attacker saw that I “just woke up” he incorrectly assumed that I must be at home — he was clearly not sophisticated enough to know my routine. I can only imagine how this story may have played out differently if not for this one tiny point. Had I been home, we may not have made contact with the SWAT team until they were breaking down the door, which would have likely ended badly.
The Real Problem with SWATting
I’ve waited so long to reveal the details of this day because I wanted to take additional steps to improve my operational security. I’ve written down all of the precautions I’ve taken over the past year and intend to publish them soon.
The thing is, I was lucky that the Durham Police Department is more competent and cautious than other departments in the United States. Had a few variables been different that day, I could easily be dead.
While I certainly blame the attacker for the actions they took, my root cause analysis places the blame squarely upon law enforcement for creating an exploitable vulnerability. The militarization of police combined with nonexistent authentication creates a great environment for SWATting.
When you think about it, the asymmetry is disturbing — a single anonymous phone call can result in lethal force being deployed in a matter of minutes against an arbitrary target. A single anonymous phone call costs only a few dollars to make and yet can consume tens if not hundreds of thousands of dollars in public resources just to determine whether or not a threat is real.
What’s the solution? While I’m a huge privacy advocate, I don’t think it should be possible for someone to deploy lethal force with no risk to themselves. At the very least, you should have to put your reputation on the line so that you can be held accountable. My recommendation to law enforcement agencies:
- Realize that SWATters are almost always going to place a call from outside of their target’s locale. As such, they can’t actually call 911 — they have to find a non-emergency number they can call that will escalate them to 911. These escalations should be red flagged as suspicious.
- Trace the source of the phone call; if it traces back to a completely different state than the caller’s claimed location, red flag!
- If the source phone number of the caller isn’t registered in their name (or anyone’s name) then ask for proof of identification. If the caller refuses to identify themselves (my attacker hung up when asked) then it’s a red flag!
I leave you with an excerpt from The Crypto Anarchist Manifesto, emphasis mine:
Computer technology is on the verge of providing the ability for individuals and groups to communicate and interact with each other in a totally anonymous manner. Two persons may exchange messages, conduct business, and negotiate electronic contracts without ever knowing the True Name, or legal identity, of the other. Interactions over networks will be untraceable, via extensive re- routing of encrypted packets and tamper-proof boxes which implement cryptographic protocols with nearly perfect assurance against any tampering. Reputations will be of central importance, far more important in dealings than even the credit ratings of today. These developments will alter completely the nature of government regulation, the ability to tax and control economic interactions, the ability to keep information secret, and will even alter the nature of trust and reputation.



